Why Post-Quantum Planning Should Start Before It Feels Urgent
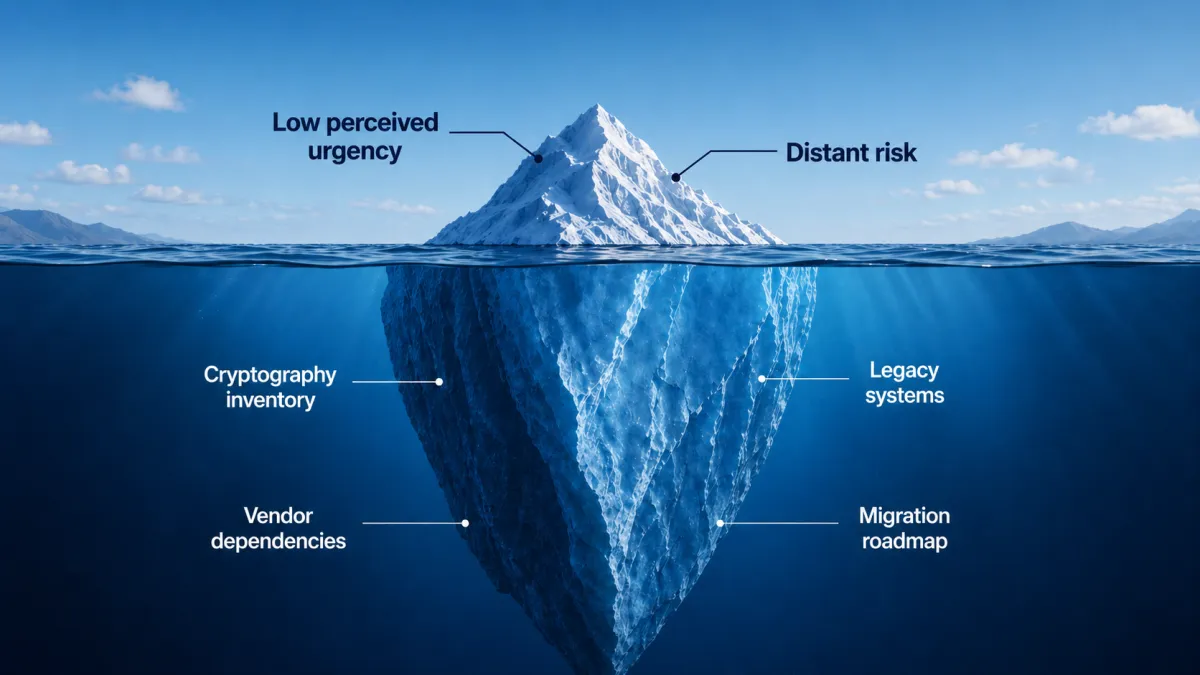
An iceberg is often misunderstood. The visible portion above the waterline draws attention, but the larger and more consequential mass remains hidden below the surface.
Post-quantum cybersecurity presents a similar leadership challenge. For many enterprise leaders, quantum risk still feels distant. It does not create the same immediate pressure as ransomware, outage risk, regulatory deadlines, or AI governance. Without an obvious disruption forcing the issue into every leadership meeting, post-quantum planning can seem important but not immediate.
That apparent lack of urgency can be misleading.
The readiness window is already open
NIST finalized its first three post-quantum cryptography standards in August 2024 and encouraged system administrators to begin integrating them because full adoption will take time. NIST also says organizations should begin applying these standards now, identify where vulnerable algorithms are used, and plan to replace or update them. (NIST)
CISA, NSA, and NIST have made the same broader point: organizations should begin preparing by creating quantum-readiness roadmaps, conducting cryptographic inventories, assessing risk, and engaging vendors. Their guidance also highlights the concern that sensitive data captured today may still need protection in the future, a risk often described as “harvest now, decrypt later.” (NCCoE)
This does not mean leaders need to panic. It means the work is no longer theoretical. Standards are available, guidance is clear, and the transition will require more than a last-minute technical update. Organizations that wait until post-quantum security feels urgent may still be able to respond, but they will likely be working under compressed timelines, incomplete inventories, unclear accountability, uneven vendor answers, and competing priorities.
What sits below the surface
The work below the waterline is not a single replacement project. Cryptography is embedded across applications, identity systems, certificates, networks, cloud services, connected devices, vendor platforms, and data protection practices. Some dependencies are visible. Others have operated quietly for years.
That is why leaders need an early view into four areas.
The first is the cryptography inventory: where public-key cryptography is used, which systems depend on it, and where vulnerable algorithms may be embedded. Without that view, the organization may not fully understand its exposure.
The second is legacy systems. Older applications, devices, infrastructure, and processes may be difficult to update quickly, especially when ownership is unclear, documentation is limited, or the system supports critical operations.
The third is vendor dependencies. Most enterprises rely on software providers, cloud platforms, managed services, hardware suppliers, and third-party tools that will influence the timing and clarity of any migration.
The fourth is the migration roadmap, which connects the other pieces. It defines ownership, sequencing, prioritization, governance, and the path from awareness to action.
Together, these areas make post-quantum planning an enterprise readiness issue, not just a cybersecurity concern. The business impact can extend to customer trust, regulatory posture, contractual obligations, data retention practices, business continuity, and the ability to protect information that may remain sensitive long after it is created.
Start before the pressure arrives
The better first move is not buying a tool. It is building a readiness view.
Enterprise leaders can begin with practical questions:
Where do we rely on vulnerable cryptography today?
Which systems are most critical or hardest to update?
Which data needs to remain sensitive for years?
Which vendors will influence our timeline?
Who owns the readiness roadmap?
How will we prioritize the highest-risk areas first?
These questions do not require panic. They require disciplined leadership.
The visible tip of post-quantum risk may still look small, but the work below the waterline is not. Planning should start before the issue feels urgent because readiness takes longer than urgency allows. Organizations that handle this transition well will be the ones that begin early enough to understand what lies beneath the surface, assign ownership, and plan before pressure becomes unavoidable.
